Quick filters:
Software protection Stock Photos and Images
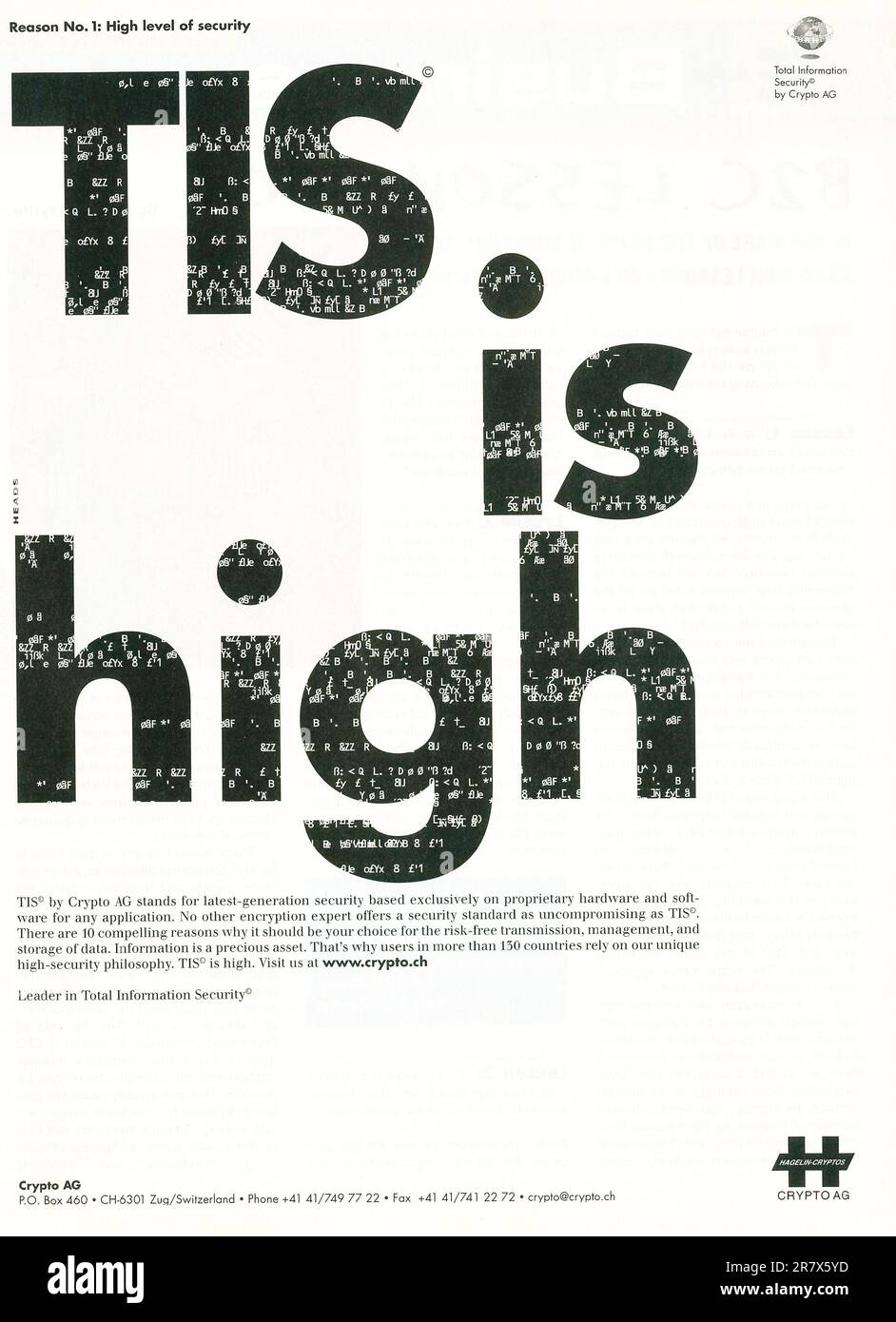
RM2R7X5YD–Crypto AG Crypto company advert in a magazine 2001. Crypto AG was a Swiss company specialising in communications and information security

RF2HDHHNR–encryption, firewall, antivirus software, protection, encryptions, firewalls, antivirus softwares, computer software

RF2RT3GDP–Ostersund, Sweden - Mars 20 2023: AVG Antivirus website on a computer screen. AVG Antivirus is a line of antivirus software developed by AVG Technolog
RF3CFKY8D–Cyber security data protection concept. Professional using a laptop with virtual protective shield, depicting online data security cyber protection
RF2WHBW8H–Businessman using computer secure encryption technology, cybersecurity privacy of data protection, security Internet access, security encryption of us

RFJ22AJM–Business, Technology, Internet and network concept. Young business man, working on the tablet of the future, select on the virtual display: Internet S

RFMNR2WC–Press enter button on the keyboard computer Protective shield virus red Exclamation Warning Caution Computer in dark with word virus

RFW0H32D–Professional Development programmer cooperating meeting and brainstorming and programming website working in a software and coding technology, writing
RF2H5KBA7–Data protection, privacy information. Hand holding mobile phone with shield. Cyber security network, internet technology concept

RF2G7P1N8–Coder programmer hacker coding cyber attack computer network information protection security
RFM0JGRD–Concept of antivirus, system protection and cybersecurity. Vaccination in the syringe on computer keyboard.

RF2X0HGXA–cybersecurity concept. biometric security software, protection of private information. Fingerprint identification.
RF3BKRYYT–Antivirus software preventing malware from infecting system symbolized by wooden cubes with red prohibition sign on blue background
RF2X6746B–Close-up Focus on Person's Hands Typing on the Desktop Computer Illuminated Keyboard. Screens Show Coding Language User Interface. Software Engineer Create Innovative Commerce App. Program Development

RF2H2TXRJ–Software protection dongle concept with Random Parts of Program Code.Software protection dongle text written on Programming code abstract technology b
RM3D3B9BF–November 4, 2024, Brazil. In this photo illustration, the AVG Protection app logo is displayed on a smartphone screen
RF2YYJW21–New York, USA - December 21, 2024: Check Point Software website homepage displayed on laptop screen with logo. Cybersecurity company offering advanced
RF3BHT0YK–Poznan, Poland - June 6, 2025: Windows Security application shown on a computer screen, presenting privacy and digital protection features for users o

RF2Y9RHWC–Future technology with hologram protection interface. Internet security and data protection concept. Blockchain and cybersecurity.
RF3DX9BGK–Windows security interface showing virus and threat protection status with green checkmark icon, cybersecurity software monitoring and digital safety
RF2HPXXWK–Locked metal padlock on a laptop keyboard over blue background. Cyber security, antivirus software concept.
RFME4752–Cyber internet security system. Lock icon technology on computer laptop screen with application icons

RFP9GP5T–blocks of binary data. Blockchain concept. blue background with computer digital binary code bit number one and zero text. selective focus.
RF2YBTEPN–Concept of cloud computing technology. Protecting data and servers remotely. Network connection.Innovative startup project.
RF2X7TK6G–Man, dark background and tablet for cybersecurity with software update for scammer protection. Cybercrime, digital app and internet connection on
RFJACTJ4–Smart phone in chain with lock. Isolated on white with clipping path. Security, data protection and software lock theme
RM2HE0R00–McAfee antivirus protection pop-up message on a laptop computer screen. Online security software.
RM2J7BH90–Concept of hacking and malware. Hacker using an abstract laptop with a binary code digital interface. Young hacker in cybersecurity concept.
RF2DJ65R7–Business man with icon Cyber crime and protecting data personal information on tablet. Internet technology networking connection. Data protection priv
RF2WPJHCD–cyber security icon with marking on world map on businessman hand shake security join world wild
RF2E41WG3–Open lock symbol on a computer screen - protection of personal data and digital information
RF2T7F7G2–Coder or hacker. Data programmer, developer or engineer in office. Cyber crime security software for fraud and theft online.
RF3DCA5TY–Healthcare professional interacting with digital security icons representing data protection, secure communication, patient privacy, medical informati

RF2MNHTH6–Online cyber social security internet cyberspace law rules rights regulation security lock protection against copyrights misuse conduct, social media

RF2H97TB0–female hand holds a piece of paper with the inscription Data Security and lock symbol in green writing over dark green background with binary code
RF2R0B9BX–Close-up of a man's hands on a laptop keyboard. Concept the development of antivirus, cybersecurity, data protection, firewall applications
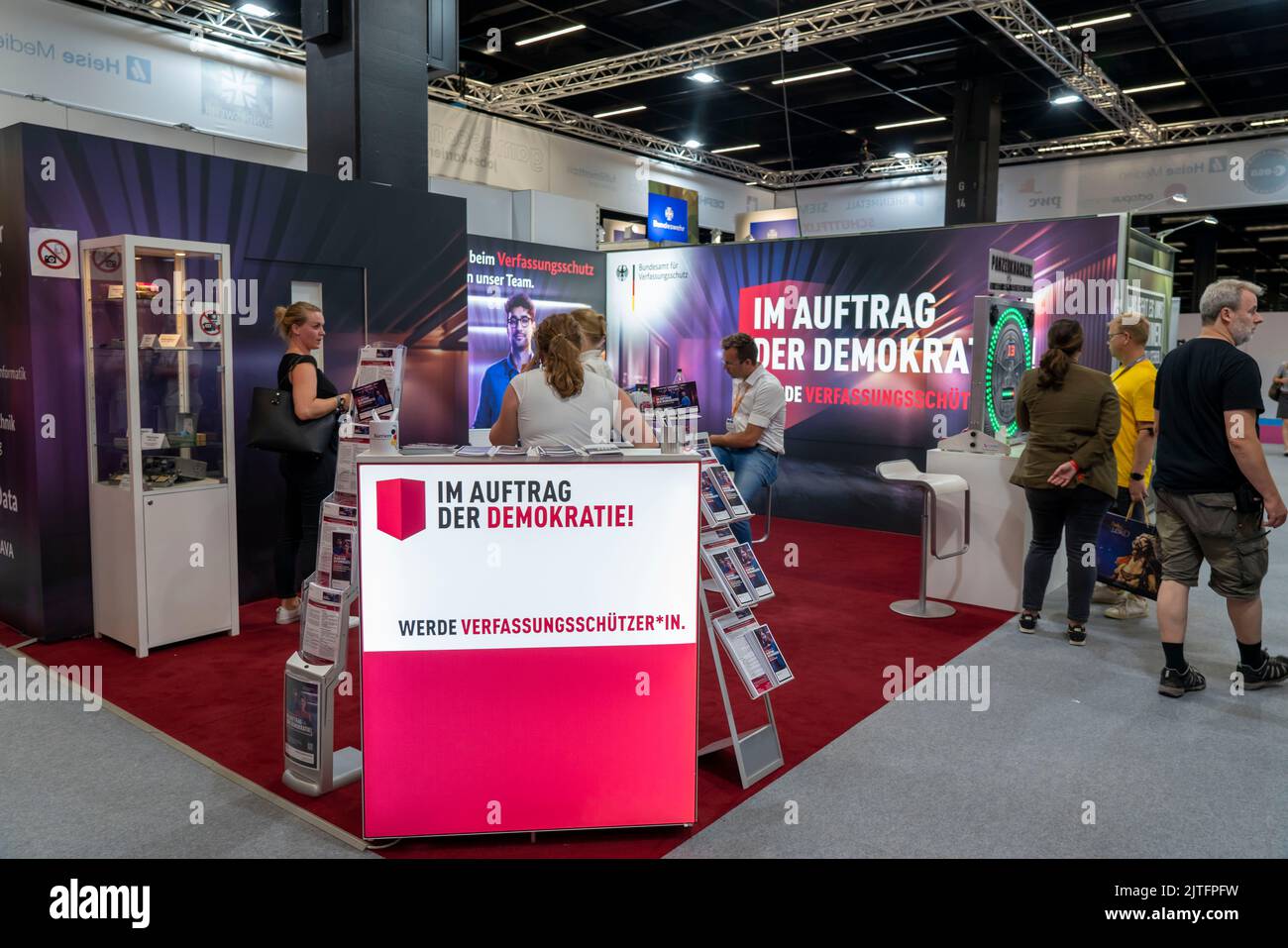
RM2JTFPFW–Gamescom, the world's largest trade fair for video and computer games, stand of the Federal Office for the Protection of the Constitution, in Cologne,
RF2SCAAED–Businesswoman typing in computer. bug detection and online security, hacker attack and cyber crime. Concept of virus, digital protection and software
RF2PT3HG2–System being hacked, compromised software environment. Darkweb, darknet and hacking concept.
RF3DTN61R–Software developer programming python code for AI. Web development with HTML and cybersecurity for data protection. Programmer working on futuristic v
RF3D3F0RH–Cybersecurity defense and system protection from hackers, secure digital systems, cyberattack prevention, IT security solutions, and risk mitigation
RF2AWJMH1–Developing programming and coding technologies. Website design. Programmer working in a software develop company office.
RF2S5HP19–Man in suit working on laptop, digital tablet. Cyber security shield, lock. Glowing icons of computer alerts, folders. Protection of sensitive data

RF2MNJJKY–Big date. Concept Data storage, world wide web, media, internet, cloud storage, data protection. Visualization of artificial intelligence in data
RF2H4R89E–Security system is compromised and is falling apart. Corporate data leakage. Hacker attack. Search for software vulnerabilities. Violation of integrit

RF2K0PPB5–Protection of information. Login check. Digital technology, internet connection. Login control and archiving software.

RF3DX7G7J–Cybersecurity and privacy concepts, data protection and encryption of secure internet networks

RFPKH0N5–Woman hacker is ready to run malware program virus on the internet. Start hacking remote system computer

RFH2D0BK–Cybercriminal concept. Keychain handcuffs on the computer keyboard. Police lights luminosity.

RF2X2FT9C–A Trojan Horse is a computer program designed to breach the security of a computer system while ostensibly performing some innocuous function.
RM2WR0J69–1998 At&T WorldNet service with Kids CyberHighway and CyperPatrol service ad. "Teach them how to surf."
RF2J9C0YK–KONSKIE, POLAND - May 21, 2022: www.veeam.com website displayed on laptop screen. Veeam Software is IT data protection company
RF2YPFW96–Ostersund, Sweden - Oct 20, 2024. Avira webpage. Avira is a German multinational computer security software.
RF3C13RJ6–Data breach cybersecurity vulnerability. Warning alert system concept, system hacked on computer network, cybercrime and virus, Malicious software,
RF2SE4C89–Cyber security and data protection on internet, Password protected system and storage, Cybersecurity technology, Person touching virtual shield, Secur

RFJ22AN0–Business, Technology, Internet and network concept. Young business man, working on the tablet of the future, select on the virtual display: Data Encry